


Senior security engineer focused on product security, cloud infrastructure testing, and vulnerability management. Define the methodology, own the pipeline, and make sure nothing ships with a hole in it. Use AI tooling because it actually makes the work better, not as a checkbox. 120+ bug bounty vulnerabilities on HackerOne.

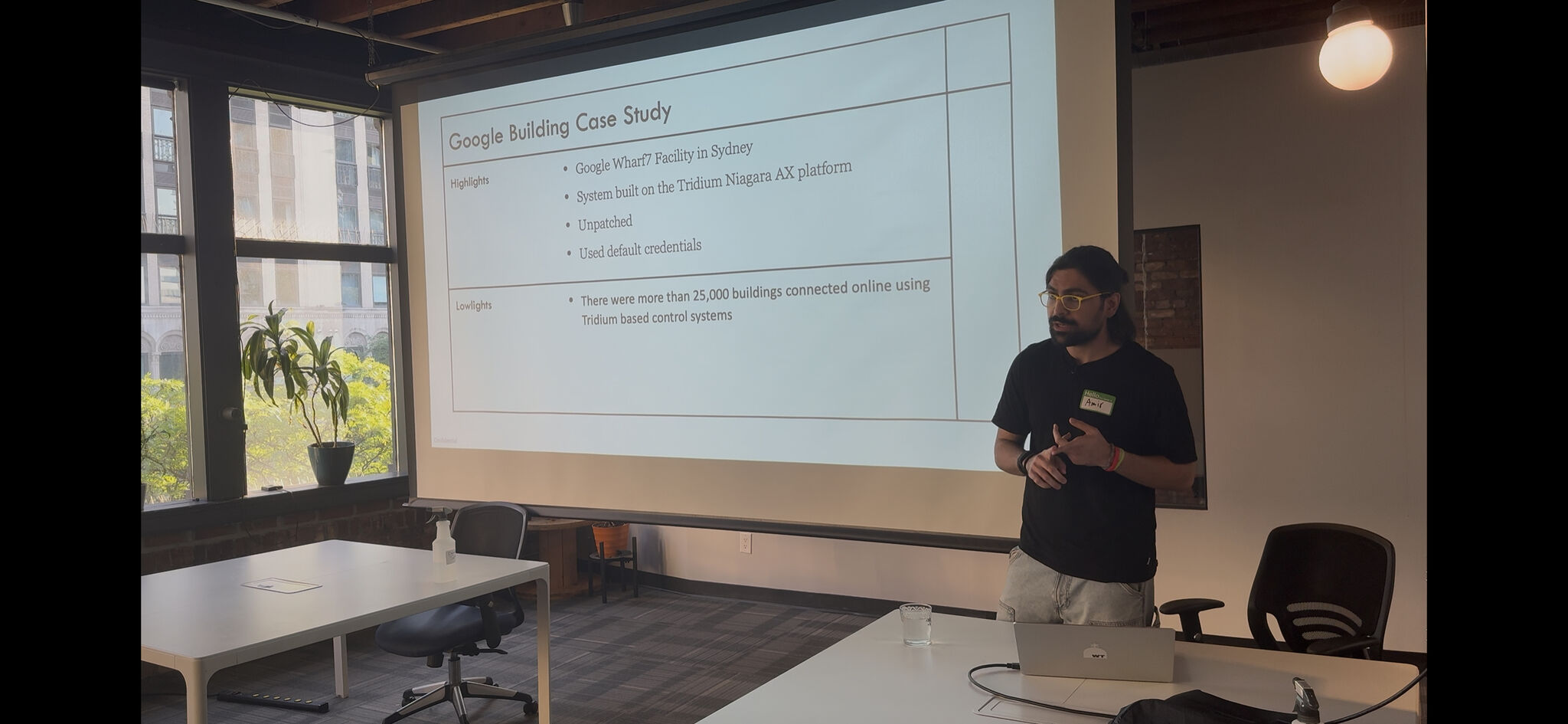


Product security and penetration testing for enterprise environments. Web applications, APIs, cloud infrastructure, containers. The work is time sensitive because it sits in the release cycle. Test fast, find what matters, report it clearly, and move on.
The part most people skip is the pipeline. Findings come in from pentests, scanners, and external researchers. Someone needs to triage, validate, prioritize, and make sure product teams understand what to fix and why. That is where most of my value sits. Not just finding bugs, but running the process that turns findings into fixes.
120+ validated vulnerabilities on HackerOne. That research keeps me sharp on what real attack surfaces look like in production, not in a lab.
Before testing starts, develop deep technical understanding of the feature, the architecture, and the threat model. Testing without context is just scanning with extra steps.
Claude and Gemini are part of the daily workflow. Recon automation, config analysis, attack vector generation, report drafting. Not a gimmick. Cuts hours off repetitive work so time goes to the findings that actually matter.
Testing is half the job. The other half is making sure findings get triaged, prioritized, and communicated so product teams act on them before the next release window closes.
Testing: Web apps, APIs (REST, WebSockets, GraphQL), cloud infra, containers, Terraform
Cloud: AWS, GCP, Azure, Cloudflare, Kubernetes (GKE, EKS, ECS)
Tools: Burp Suite Pro, Nuclei, Metasploit, Nmap, Wireshark
AI: Claude, Gemini, prompt engineering for security workflows
Languages: Python, Go, Bash
Frameworks: OWASP Top 10, MITRE ATT&CK, NIST, CVSS
Product security engineer who owns the methodology and the pipeline.